Journalists often work with sensitive data, which they need to protect well in case an adversary searches their electronic device. In this article, tech security expert Bence Kócsi explains for Reporters Without Borders (RSF) how to create a decoy system to hide sensitive material.
In their work, journalists have to protect the sensitive data they collect, notably their sources’ identifying information. The best technique to protect sensitive data is to hide it without seeming to hide it, in other words by convincing an adversary searching their device that there is nothing of value on it.
A decoy system is any operating system, file system, folder, or information on a device which is designed to appear real and of interest to an adversary, but which contains no information of any value. Meanwhile, the sensitive information is stored either out of sight of intruders, or in places they would not look.
The point of a decoy system is not just to hide the sensitive data, but to convince an adversary that there is nothing being hidden at all. Decoy systems must therefore look normal, busy, and “lived in.” There should be apps installed, projects in progress, and a history of usage. For journalists, there should be research notes, video evidence, draft articles etc. that an intruder will be looking for. A system which is too clean will likely tip-off the intruder that something is hidden.
“Hidden” files on the computer
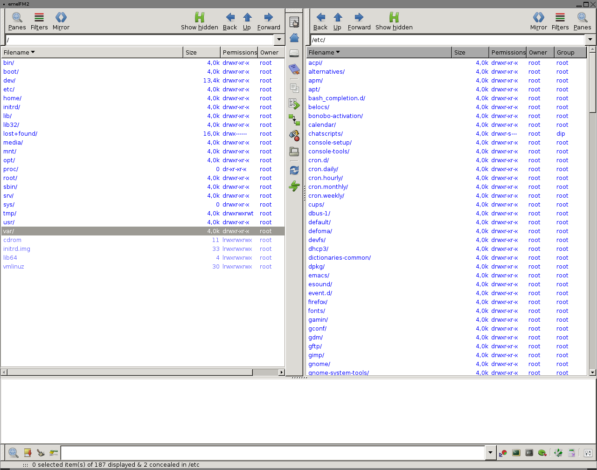
Most file explorers have a feature which hides files the user is unlikely to need to access, such as system files. This feature also allows users to set files and entire folders in “hidden” locations. Journalists can use this to create a file system on their devices which, at a glance, appears to be free of any sensitive information. Be careful though – file explorers can be instructed to “show hidden files” at the click of a button, so journalists should take extra safety steps:
- Denominate hidden files with names that look like system files. For example, agm64.sys, ext12.bin, app_client.exe, or NH4_view.dll.
- Store hidden files in folders which contain legitimate files. An empty folder is suspicious, as even a hidden file will be counted toward the folder’s size.
- Hide files and directories directly at the system level following this guide if needs be — the handling is more tech-savvy but also more effective.
Decoy apps on smartphones
Most phones have built-in settings to hide files and apps out of immediate sight (see these guides for Apple and Android). Additionally, many decoy apps exist for smartphones.
For instance, this app appears as a calculator app, but is actually a vault, storing files securely behind a PIN and away from prying eyes. Apps such as this can be spotted as fake on close inspection, but at first glance offer a cheap and easy way to keep intruders from finding sensitive information on a phone.
However many such apps are for-profit, and have ads and paid premium versions, and some have presented security concerns themselves, therefore always research apps thoroughly before entrusting them with sensitive data.
A hidden dual-boot
Computers can have two operating systems (OS) installed at once, typically Windows and Linux. When the computer is turned on, it gives the user the choice which OS they want to use, and the two exist independently of each other.
A hidden dual-boot is when the computer is set up to automatically boot a particular OS unless the user intervenes, and hides the choice screen altogether. This means an intruder would not immediately know a second OS was even installed and would only search the decoy OS used as a decoy, with no sensitive information on it.
Bence Kócsi is an experienced freelance editor, writer, and researcher. He has been focusing on a wide range of topics including digital security, technology, historical linguistics, politics, and medicine.